Remote IoT Monitoring via SSH: A Comprehensive Guide
In the rapidly evolving world of technology, Remote IoT Monitoring via SSH has become an essential tool for businesses and individuals alike. It allows users to securely access and manage IoT devices from any location, ensuring seamless connectivity and efficient monitoring. This technology is transforming how we interact with smart devices, providing unparalleled convenience and control.
As the Internet of Things (IoT) continues to expand, the need for secure and reliable remote access solutions becomes increasingly important. SSH, or Secure Shell, plays a pivotal role in ensuring that data transmission remains encrypted and protected from unauthorized access. Whether you're managing a network of smart home devices or overseeing industrial IoT systems, understanding Remote IoT Monitoring via SSH is crucial.
This article will delve into the intricacies of Remote IoT Monitoring via SSH, exploring its benefits, applications, and best practices. By the end, you will have a comprehensive understanding of how this technology works and how it can be leveraged to enhance your IoT infrastructure.
Introduction to SSH
SSH, or Secure Shell, is a cryptographic network protocol designed to provide secure communication over an unsecured network. It is widely used for remote login and other secure network services. SSH ensures that data transmitted between devices is encrypted, making it nearly impossible for malicious actors to intercept sensitive information.
Key Features of SSH
SSH offers several key features that make it ideal for remote IoT monitoring:
- Encryption: All data transmitted via SSH is encrypted, ensuring confidentiality.
- Authentication: Users must authenticate before gaining access to a device, adding an extra layer of security.
- Integrity: SSH ensures that data has not been tampered with during transmission.
These features make SSH a trusted choice for secure remote access, especially in the realm of IoT devices.
IoT Monitoring Basics
IoT monitoring involves tracking and analyzing data generated by interconnected devices. These devices can range from simple sensors to complex industrial machinery. Effective IoT monitoring ensures that devices are functioning optimally and alerts users to any anomalies or issues.
Importance of IoT Monitoring
The importance of IoT monitoring cannot be overstated. It provides:
- Real-time insights into device performance.
- Early detection of potential problems, reducing downtime.
- Optimization of resource usage and energy efficiency.
By leveraging IoT monitoring, organizations can enhance their operational efficiency and make data-driven decisions.
Remote IoT Monitoring
Remote IoT monitoring allows users to access and manage IoT devices from anywhere in the world. This capability is particularly valuable for businesses with geographically dispersed operations. By using SSH for remote IoT monitoring, users can ensure that their devices remain secure and functional, regardless of their physical location.
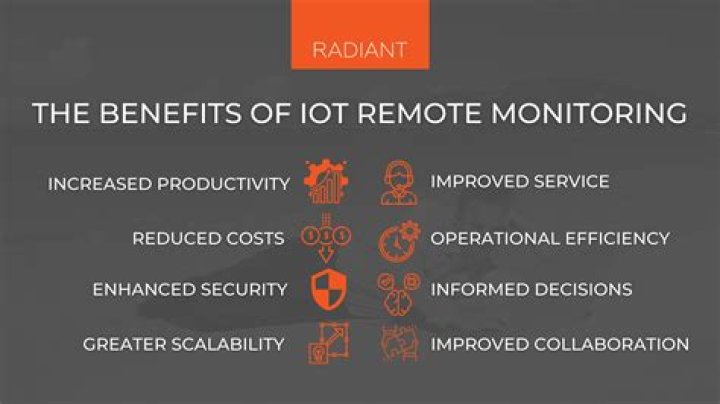
Benefits of Remote IoT Monitoring
Some of the key benefits of remote IoT monitoring include:
- Increased flexibility in device management.
- Reduced need for on-site maintenance, saving time and resources.
- Enhanced security through encrypted connections.
These advantages make remote IoT monitoring via SSH an indispensable tool for modern businesses.
Why Use SSH for Remote IoT Monitoring?
SSH is the preferred protocol for remote IoT monitoring due to its robust security features and ease of use. Unlike other protocols, SSH provides end-to-end encryption, ensuring that sensitive data remains protected. Additionally, SSH supports various authentication methods, including public key authentication, which enhances security further.
Comparison with Other Protocols
When compared to other protocols like Telnet or FTP, SSH stands out for its:
- Strong encryption protocols.
- Support for secure file transfers.
- Compatibility with a wide range of devices and operating systems.
These advantages make SSH the go-to choice for secure remote IoT monitoring.
Security Benefits of SSH
One of the primary reasons for using SSH in remote IoT monitoring is its strong security features. SSH employs advanced encryption algorithms to protect data during transmission. This ensures that even if a malicious actor intercepts the data, they will not be able to decipher it without the encryption key.
How SSH Enhances Security
SSH enhances security in several ways:
- By encrypting all data transmitted between devices.
- Through strong user authentication mechanisms.
- By preventing unauthorized access to IoT devices.
These security measures are critical in protecting sensitive data and ensuring the integrity of IoT networks.
Implementation Steps for Remote IoT Monitoring via SSH
Implementing remote IoT monitoring via SSH involves several key steps. These steps ensure that the system is secure, efficient, and easy to manage. Below is a step-by-step guide:
Step 1: Install SSH on IoT Devices
The first step is to install SSH on the IoT devices you wish to monitor. Most modern IoT devices come with SSH pre-installed, but if not, you can install it manually.
Step 2: Configure SSH Settings
Once SSH is installed, configure the settings to meet your security requirements. This includes setting up strong passwords and enabling public key authentication.
Step 3: Connect to Devices Remotely
With SSH configured, you can now connect to your IoT devices remotely. Use an SSH client to establish a secure connection and begin monitoring your devices.
By following these steps, you can set up a secure and efficient remote IoT monitoring system using SSH.
Common Challenges in Remote IoT Monitoring via SSH
While SSH offers many advantages for remote IoT monitoring, there are also some challenges that users may encounter. These challenges include:
Network Connectivity Issues
Poor network connectivity can disrupt SSH sessions, leading to interrupted monitoring. To mitigate this, ensure that your devices have a stable internet connection.
Authentication Failures
Authentication failures can occur if passwords or keys are incorrect. Regularly review and update authentication credentials to prevent such issues.
Data Latency
Data latency can affect the speed and accuracy of monitoring. Optimize your network settings to minimize latency and ensure real-time data transmission.
Addressing these challenges is essential for maintaining a reliable remote IoT monitoring system.
Best Practices for Secure Monitoring
To ensure the security and efficiency of your remote IoT monitoring system, follow these best practices:
Regular Updates and Patches
Keep your SSH software and IoT devices updated with the latest security patches. This helps protect against vulnerabilities and ensures optimal performance.
Strong Password Policies
Enforce strong password policies to prevent unauthorized access. Use complex passwords and change them regularly.
Monitor System Logs
Regularly review system logs to detect any suspicious activity. This proactive approach can help identify and address security threats before they escalate.
By adhering to these best practices, you can enhance the security and reliability of your remote IoT monitoring system.
Real-World Applications of Remote IoT Monitoring via SSH
Remote IoT monitoring via SSH has numerous real-world applications across various industries. Some notable examples include:
Smart Home Automation
Homeowners can remotely monitor and control smart home devices, ensuring optimal performance and energy efficiency.
Industrial IoT
Manufacturing plants use remote IoT monitoring to track the performance of machinery and equipment, reducing downtime and improving productivity.
Agriculture
Farmers utilize remote IoT monitoring to track soil moisture levels, weather conditions, and crop health, enabling data-driven decision-making.
These applications demonstrate the versatility and value of remote IoT monitoring via SSH in various sectors.
Future Trends in Remote IoT Monitoring
The future of remote IoT monitoring via SSH is promising, with several trends shaping its development. These trends include:
Increased Use of AI and Machine Learning
AI and machine learning are being integrated into IoT monitoring systems to enhance predictive analytics and automation.
5G Connectivity
The rollout of 5G networks will significantly improve the speed and reliability of remote IoT monitoring, enabling real-time data transmission.
Edge Computing
Edge computing allows data processing to occur closer to the source, reducing latency and improving efficiency in IoT monitoring.
These trends will continue to drive innovation in remote IoT monitoring via SSH, offering new opportunities for businesses and individuals alike.
Conclusion
Remote IoT Monitoring via SSH is a powerful tool that offers secure and efficient access to IoT devices from anywhere in the world. By understanding its benefits, applications, and best practices, you can leverage this technology to enhance your IoT infrastructure and improve operational efficiency.
We encourage you to implement the steps outlined in this article and explore the real-world applications of remote IoT monitoring via SSH. Don't forget to share your thoughts and experiences in the comments below, and consider exploring other articles on our site for more insights into IoT technology.