Mastering RemoteIoT VPC SSH: A Comprehensive Guide to Secure Downloads
RemoteIoT VPC SSH download has become an essential aspect for organizations looking to enhance their network security and efficiency. With the increasing reliance on cloud-based infrastructure, understanding how to configure and manage Virtual Private Clouds (VPC) with Secure Shell (SSH) protocols is critical. This guide will delve into the intricacies of RemoteIoT VPC SSH and provide you with actionable insights to streamline your network operations.
As more businesses transition to remote work models, the importance of secure communication channels cannot be overstated. RemoteIoT VPC SSH serves as a robust solution for connecting devices and networks securely, ensuring data integrity and confidentiality. This article aims to equip you with the knowledge and tools necessary to implement and optimize your RemoteIoT VPC SSH configurations.
Whether you're a network administrator, IT professional, or simply someone interested in enhancing your cybersecurity skills, this comprehensive guide will walk you through every step of the process. From understanding the basics of VPC SSH to advanced configuration tips, we've got you covered.
Table of Contents
Introduction to RemoteIoT VPC SSH
Understanding Virtual Private Cloud (VPC)
What is SSH and Why It Matters
Setting Up VPC SSH for RemoteIoT
Security Best Practices for VPC SSH
Common Issues and Troubleshooting
Optimizing VPC SSH Performance
Real-World Use Cases of RemoteIoT VPC SSH
Introduction to RemoteIoT VPC SSH
RemoteIoT VPC SSH represents a cutting-edge solution for managing secure communications between devices and networks. In today's digital landscape, where cybersecurity threats are prevalent, having a secure and reliable method for accessing and managing remote devices is paramount. VPC SSH acts as a bridge, enabling seamless and encrypted connections between IoT devices and cloud-based infrastructure.
Virtual Private Clouds (VPCs) provide isolated network environments where organizations can deploy and manage their resources securely. By integrating SSH into VPC configurations, businesses can ensure that all communications are encrypted and protected from unauthorized access. This setup is particularly beneficial for IoT applications, where multiple devices need to communicate securely over the internet.
Understanding the fundamentals of RemoteIoT VPC SSH is crucial for anyone involved in network management or cybersecurity. This section will lay the groundwork for more advanced topics, ensuring you have a solid foundation to build upon.
Understanding Virtual Private Cloud (VPC)
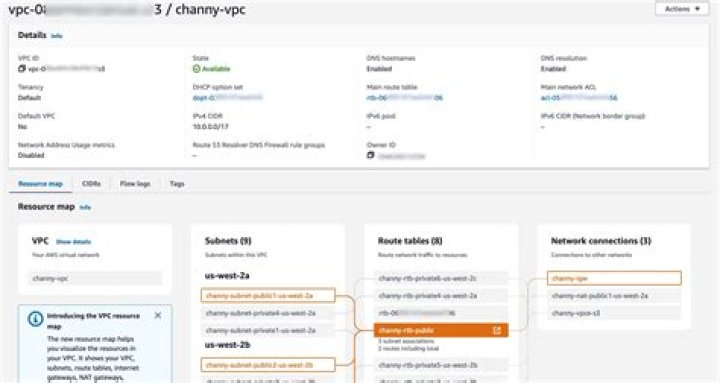
A Virtual Private Cloud (VPC) is a logically isolated section of a public cloud where users can launch resources in a virtual network they define. VPCs offer enhanced security, flexibility, and control over your cloud environment. By creating a VPC, you can specify your own IP address range, create subnets, and configure route tables and network gateways.
Key Features of VPC:
- Private Subnets: Isolate resources within your network for added security.
- Public Subnets: Allow resources to communicate directly with the internet.
- Internet Gateway: Enable communication between your VPC and the internet.
- Security Groups: Act as virtual firewalls to control inbound and outbound traffic.
By leveraging VPCs, organizations can create a secure and scalable environment for deploying their applications and services. Understanding how VPCs work is essential for effectively integrating SSH protocols into your network infrastructure.
Benefits of Using VPC
Using a VPC provides numerous advantages, including:
- Enhanced Security: Isolate resources and control access to ensure data protection.
- Scalability: Easily scale your resources up or down based on demand.
- Customization: Define your own IP address range and subnet configurations.
What is SSH and Why It Matters
Secure Shell (SSH) is a cryptographic network protocol designed for secure data communication, remote command execution, and other secure network services. SSH ensures that all data transmitted between devices is encrypted, protecting it from interception and tampering. This protocol is widely used in network administration and is a cornerstone of modern cybersecurity practices.
Key Features of SSH:
- Encryption: Encrypts all data transmitted between devices, ensuring confidentiality.
- Authentication: Verifies the identity of users and devices to prevent unauthorized access.
- Integrity: Ensures that data has not been altered during transmission.
In the context of RemoteIoT VPC SSH, SSH plays a critical role in securing communications between IoT devices and cloud-based infrastructure. By implementing SSH, organizations can safeguard their networks from potential threats and vulnerabilities.
What is RemoteIoT?
RemoteIoT refers to the practice of managing and monitoring IoT devices remotely. With the proliferation of IoT devices in various industries, the ability to access and control these devices from anywhere in the world has become increasingly important. RemoteIoT solutions enable organizations to streamline their operations, reduce costs, and improve efficiency.
Integrating VPC SSH into RemoteIoT setups ensures that all communications between devices and networks are secure and reliable. This setup is particularly beneficial for industries such as healthcare, manufacturing, and transportation, where real-time data monitoring and analysis are critical.
Key Components of RemoteIoT
The following components are essential for a successful RemoteIoT implementation:
- IoT Devices: Sensors, actuators, and other devices that collect and transmit data.
- Cloud Infrastructure: Platforms such as AWS, Azure, or Google Cloud that host and process IoT data.
- Network Connectivity: Reliable and secure connections between devices and cloud infrastructure.
Setting Up VPC SSH for RemoteIoT
Setting up VPC SSH for RemoteIoT involves several steps, including configuring your VPC, setting up SSH keys, and establishing secure connections. Below is a step-by-step guide to help you get started:
- Create a VPC: Define your IP address range and create subnets for your resources.
- Set Up SSH Keys: Generate SSH keys to authenticate users and devices.
- Configure Security Groups: Define rules for inbound and outbound traffic.
- Launch Instances: Deploy instances within your VPC and configure SSH access.
By following these steps, you can ensure that your RemoteIoT VPC SSH setup is secure and functional. Refer to official documentation from cloud providers for more detailed instructions.
Best Practices for VPC SSH Configuration
When configuring VPC SSH, consider the following best practices:
- Use strong SSH keys and avoid password-based authentication.
- Limit access to specific IP addresses or ranges.
- Regularly update and patch your systems to address vulnerabilities.
Security Best Practices for VPC SSH
Ensuring the security of your RemoteIoT VPC SSH setup is paramount. Below are some best practices to help you protect your network from potential threats:
- Use Multi-Factor Authentication (MFA): Add an extra layer of security by requiring multiple forms of verification.
- Monitor Logs: Regularly review logs for suspicious activity and take appropriate action.
- Limit Access: Restrict access to only authorized users and devices.
By implementing these best practices, you can significantly enhance the security of your RemoteIoT VPC SSH setup and protect your network from potential attacks.
Common Security Threats
Some common security threats to be aware of include:
- Brute Force Attacks: Unauthorized attempts to guess SSH passwords.
- Man-in-the-Middle Attacks: Intercepting communications between devices.
- Malware: Malicious software designed to disrupt or damage systems.
Common Issues and Troubleshooting
Despite careful planning and implementation, issues may arise when setting up RemoteIoT VPC SSH. Below are some common problems and solutions:
- Connection Issues: Ensure that security groups and network ACLs allow SSH traffic.
- Authentication Failures: Verify that SSH keys are correctly configured and match between devices.
- Performance Bottlenecks: Optimize your VPC configuration and monitor resource usage.
If you encounter any issues, refer to the official documentation or seek assistance from community forums and support channels.
Optimizing VPC SSH Performance
Optimizing the performance of your RemoteIoT VPC SSH setup can lead to improved efficiency and reduced latency. Below are some tips for optimizing performance:
- Use High-Speed Connections: Ensure that your network infrastructure supports fast and reliable connections.
- Load Balancing: Distribute traffic evenly across multiple instances to prevent overload.
- Cache Data: Store frequently accessed data locally to reduce the need for repeated downloads.
By implementing these optimization techniques, you can enhance the performance of your RemoteIoT VPC SSH setup and ensure seamless operations.
Tools for Performance Monitoring
Consider using the following tools for monitoring and optimizing performance:
- CloudWatch: Monitor metrics and set alarms for your AWS resources.
- Prometheus: Collect and analyze performance data from your systems.
- Grafana: Visualize performance data and gain insights into system behavior.
Real-World Use Cases of RemoteIoT VPC SSH
RemoteIoT VPC SSH has numerous real-world applications across various industries. Below are some examples:
- Healthcare: Securely monitor patient data and medical devices.
- Manufacturing: Remotely control and manage industrial equipment.
- Transportation: Monitor and analyze data from vehicles and infrastructure.
By leveraging RemoteIoT VPC SSH, organizations can improve their operations, reduce costs, and enhance security.
Conclusion and Next Steps
In conclusion, mastering RemoteIoT VPC SSH is essential for anyone involved in network management or cybersecurity. By understanding the fundamentals of VPCs and SSH, configuring your setup correctly, and implementing security best practices, you can ensure the security and efficiency of your network operations.
We encourage you to take the following next steps:
- Explore official documentation for more detailed information.
- Join community forums to connect with other professionals in the field.
- Implement what you've learned and share your experiences with others.
Thank you for reading, and we hope this guide has been informative and helpful. If you have any questions or feedback, feel free to leave a comment or share this article with others who may find it useful.


